Are drones a tool for both sides in the race?
As stated in the IET technical reference: ‘Samuel Pierpont Langley is purported to have made the first successful sustained flight of an unpiloted, engine-driven heavier than air craft of substantial size on 6 May, 1896, with his Aerodrome No. 5 aircraft’. Although he was given a contract from the US Department of Defense (DoD) to develop a manned version, we don’t know the outcome and it is the Wright brothers that are credited with the first sustained, controlled, powered, heavier than air manned flight at Kill Devil Hills, North Carolina on 17 December 1903. There was little technology available and therefore the development of manned aircraft, rather than unmanned aircraft, was inevitable.
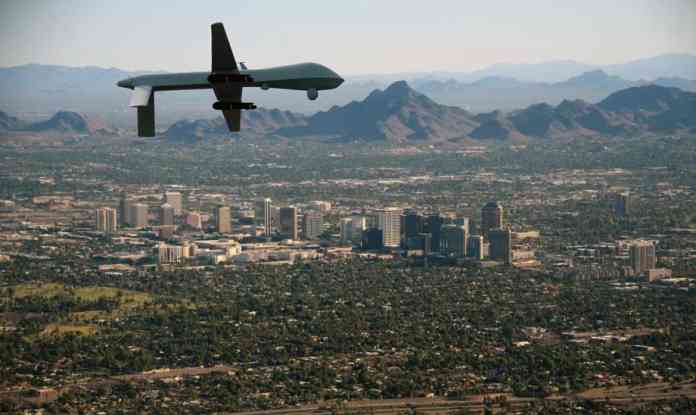
Right from the early days, and increasingly during the development advances made during WWI, manned flight undertook intelligence, surveillance and reconnaissance (ISR) roles, later developing combat roles. The developments, made possible by the advances in miniaturisation of electronics and communications, has seen the unmanned industry develop along similar lines with military ISR operations and latterly in combat roles. The use of the technologies developed for the military user are now seeing greater uptake in civilian and security services applications, police and other enforcement agencies.
In considering this article, I have concluded that I need to either provide a very scant overview or a major text of academic worth. I have, however, decided to provide an overview and explore how this technology can be utilised and the challenges that it inevitably creates. There are advantages and disadvantages to all new technologies and these must be understood before expectations can be set. However, first we need to explore what we mean by Unmanned Aerial Systems (UAS), also called Remotely Piloted Aerial Systems (RPAS). Such systems are also called ‘Drones’ and this is a legacy of the WWII use of unmanned aircraft by the Germans and refers to the unwavering low pitched sound made by the V1 engines before the fuel was exhausted and it fell to its target. This was further reinforced with the use of simple ‘Drones’ being used by armed forces for aerial target practice. Although an unflattering term that fails to reflect the technology in today’s highly sophisticated aerial systems, the name has stuck and regrettably paints an unfortunate picture for the uninitiated.
The security services tool kit
The types of system available for terrorism and counter terrorism today range from small systems weighing a few grams, handhelds and multi-rotor systems weighing less than a few kilograms and systems that resemble small aircraft. On the larger scale there are some systems available, and many more in discussion, that represent the size and capability resembling the more familiar regional jet (such as a Boeing 737 or Airbus 320). All of these are effectively conventional aircraft, but there is also a special category of UAS that is showing considerable promise and could result in a new capability to be explored - High Altitude Pseudo Satellites (HAPS). These fly at approximately 60,000ft (twice as high as most airlines) and stay airborne for months or even years at a time. They offer the possibility of persistent surveillance of a target or target area and the ability to gain long term situational awareness, understanding and intelligence.
Each of these system types has different roles within the security services ‘tool kit’. Handheld systems can operate at forward positions for on the spot information being fed back in real time to the operator ‘round the corner’. Slightly larger systems also provide tactical information and not only have longer flight time, but can operate at slightly greater ranges. These do require licenced operators and approved pilots, but it is systems in this range that perform the backbone of civil security ISR operations today. Larger systems that can operate Beyond Visual Line Of Sight (BVLOS) are deployed in a more strategic role providing a wider picture and, like in the military, ISR data is often analysed ‘off-line’. Such systems are also used in the run-up and throughout a counter terrorism operation to monitor and track suspects.
The HAPS systems are designed to give full time coverage of an area and are preplaced at a point of interest. At 60,000ft their coverage is extremely large and, even though the optical sensors can be steered on to a point of interest, the advantages are in the wider application such as border monitoring providing a wider intelligence picture.
Blurred lines
Where the technology and range of systems are available for counter terror operations the same technology is available to the terrorist. The regulations are provided by the National Aviation Authorities (CAA in UK). Legitimate users abide by these rules and the authorities enforce them.
However, where is the distinction to be drawn between limiting legitimate users ability to operate and stopping technology being available for terror intentions? This question raises many other questions. Is the automobile an ambulance or a bomb when packed with explosives? Is a Land Rover Discovery a motorway protection vehicle, a remote doctor’s vehicle of choice or military hardware? Although the colour changes so does the intention of the user. It’s not the technology but the use it is put to. It is the same with Drones. Are they looking for IEDs in Afghanistan, searching for missing walkers in the Lake District or creating havoc over central Paris? It is the same technology – different users.
Another question; is a small Drone in a city a terrorist or a recreational system out of control? So what are we trying to achieve? There is a great deal of discussion about geo-fencing, registration, licencing, and European kite marking to control and track the use of commercially available drones. It is recognised that the terrorist will build his own systems and will not comply with this type of measure. In one way he will be identifiable through the very fact that he does not comply, does not respond to a registration request, does not provide requested ground station position. This would be an improvement on the present situation but will only constitute the next step in the measure/counter-measure endless cycle. Legislation of this type will however provide yet another enforcement opportunity in the courts in the same way that US immigration forms ask if you are entering the country for terrorist purposes.
To counter this there has been research into technical ways to stop (down) an unknown or unexpected drone. These include directed energy weapons, directed EMC weapons and RF Command and Control (C2) interference – not to mention conventional munitions. However a terrorist will not be interested in rural targets where such weapons can be operated easily and trade-offs need to be considered as to the effects on the ground if these counter measures are to be used.
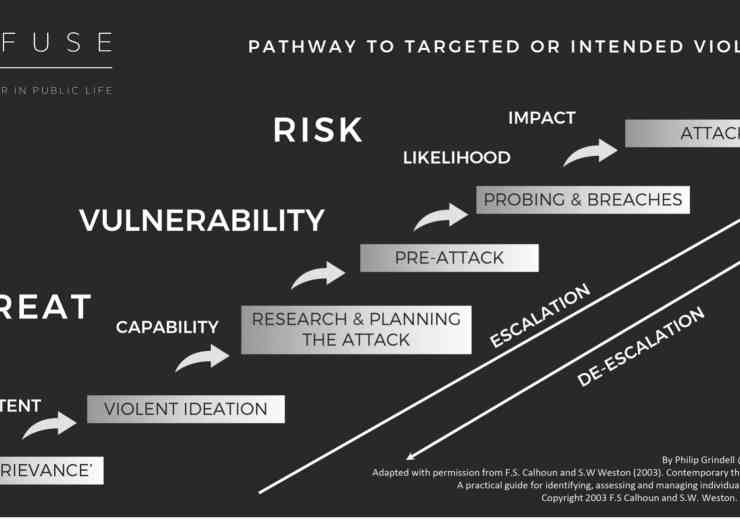
The intelligence race
In order to get a lead in this race, intelligence is important. Not data, but intelligence. Intelligence means fused data from a wide range of sources. Not what is commonly referred to as data fusion but fusion with border agency data, CAA data, police data, manufacturer’s data, airspace management data, retail data and a whole host more. Each of these agencies conducts their own data fusion but it is the combination of all these that has the potential to create a comprehensive picture of threat. There is considerable published research work being conducted into ‘big data’ but there is also work into intelligence fusion. There are many challenges in ontologies and reporting consistencies to be faced but in the counter terrorist activities associated with drone use, it provides a clear path to the information superiority necessary to gain an advantage.
Data fusion can also be used in intelligence activities with ‘on-board’ post processing of data providing a clear view of the information in a scene rather than just a raw data feed from a ‘sensor on a stick’. The use of drones in the counter terrorism picture has the potential to swamp other forms of information with data and this should be avoided. The drone is ‘a’ tool not ‘the’ tool that assists in providing information to richen the picture of events.
For the security services to be able to fully exploit the opportunities that drone technology provides, public perception needs to continue to accept the technology. There is a public nuisance created by the stories of recreational users not complying with rules and regulations but the implementation of the measures being discussed in the EU will help control this. Like any other new technology, controlling legislation always lags technological development.
Legislators need to get their head round a 100 per cent analysed world and population – big brother fears need to be understood and‑progressive thinking applied. At present, well-meaning minority activists disproportionately block the ability of the police and intelligent services to collect, store, analyse and keep data. This potentially gives the upper hand in a war of intelligence to the terror activist. In any game it is only fair if both sides play within the same rules. We have large corporates analysing our data, targeting advertising and creating profiles of almost every individual on the planet under the cover of ‘accept terms and conditions’ whereas the security services have to delete records in a specific period if they are not already part of a prosecution.
Our security services do an unprecedented job within the controls and budgets within which they have to work and public outcry should be directed at this rather than the fact that they collect the data in the first place.
Drones, UAS, RPAS; the name is not important. They are a tool for the terrorist and the security services alike. It is not the technology but the application it is put to by the operator that makes the difference. They don’t change the balance of the equation in themselves but they have the potential to give the security services a better integrated picture of the playing field through enhancing situational awareness. However they also give the terrorist the ability to act at arm’s length. It is not the technology – it is the user that makes the difference. They are a powerful tool and he that uses it best will gain best advantage.
digital issue